What is Ransomware and why it’s increasing
Most recently many businesses have transitioned their workforce to work from home, making them increasingly reliant on being digitally connected through a variety of devices. Although there are many advantages to this change, we’re also seeing some disadvantages in terms of increased ransomware attacks due to the significant growth of devices being left exposed. In the first half of 2020, ransomware attacks reached an all-time high, and we continuously hear about new attacks happening every week. What is often happening in these attacks, is the hackers are encrypting servers and files with ransomware before demanding a large sum of bitcoin in order to release the resources. These costly attacks can range from hundreds of thousands to even millions of dollars.
This frightening ongoing trend is putting all types of business on high alert and demanding that they prioritize their IT security and disaster recovery plans.
How Ransomware infects Computers, the most vulnerable entry points for Ransomware
Some of the most vulnerable entry points come from remote employees who may not be protected by their internal company firewall, they might be operating from different networks, from various different devices and likely using their residential internet and the same computer for personal and business use, this is leaving them vulnerable to ransomware attacks.
In a study completed by a ransomware negotiation company, Covewear. They found that the most common entry points for a ransomware attack are remote desktop (RDP) and phishing emails.
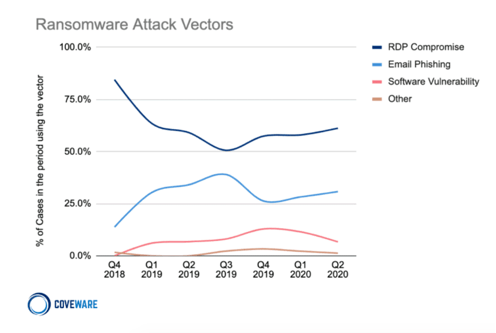
Statistics from a study completed by Coveware, a company that provides ransomware incident response and ransom negotiation services.
Remote desktop is the most common tool used for connecting to remote systems, currently there are millions of computers with remote desktop ports exposed online. Over half of the recent ransomware attacks have come from exploiting remote desktop and using remote access as an entry point.
The second most common entry point is phishing email. Cyber criminals can easily create an email that mimics legit ones sent from other business partners and embed malicious hyperlinks that once clicked can provide initial access to a network.
Protecting your business from Ransomware
How to Mitigate Ransomware Attacks
In addition to having well-trained IT teams and properly educating employees, organizations need to:
- Perform regular security patching
- Implement security features like multi-factor authentication
- Conduct email scans and filtering
- Design with security in mind
How does Veeam Backup & Disaster Recovery help protect against Ransomware?
But overall, one of the best methods to protect against ransomware attacks is to have an effective backup and disaster recovery strategy in place. This includes a robust solution that can ensure business continuity in case of an attack. By proactively implementing a Backup & Disaster Recovery solution, companies can eliminate the stress of paying the ransoms, as they can easily recover their data within a short period of time.
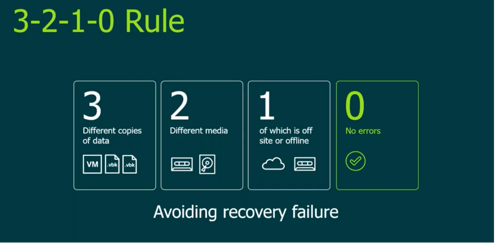
As part of a robust backup strategy, it is also recommended that organizations follow the 3-2-1 rule, and maintain 3 copies of their data (the production data and 2 backup copies) on two different media or systems with one copy off-site for disaster recovery. This offers the most optimal protection for any organization and can be a lifesaver in the case of a ransomware attack.
Although having an offsite copy of the data is great, having the off-site infrastructure on which to run your business in the event of a disaster is even better. Whipcord provides full cloud-based Disaster Recovery as a Service (DRaaS) which gives you the ability to rapidly power up the off-site copies of your production servers and resume your business from our data centre. Having these measures in place allows any organizations to restore their network with minimal downtime and without having to pay hefty ransoms to cyber criminals.
Now that you know a bit about how a ransomware attack can happen and the some of the methods to mitigate it, let’s look at the leading solution that can protect your business.
Why Choose Whipcord as your Veeam Backup & Disaster Recovery Solutions Provider
Whipcord is a leading Canadian gold partner for Veeam. We provide businesses with Veeam Backup and Disaster Recovery solutions, which are the #1 solutions on the market today. Through this offering, we enable businesses to recover data on a file level and recover servers on an individual or site-wide level and empower them to meet their RTO and RPO objectives in the case of a ransomware attack. Our methodology offers an easy, efficient way to get backups offsite to a service provider with the guarantee that your data stays in Canada in our secure and reliable data centre.
Whipcord is currently offering a free trial of the Veeam Backup, Replication and DRaaS solution to help businesses realize the value of ransomware mitigation. We encourage you to learn more about our free trials.
If you like what you’re hearing and want to start a conversation with our solutions experts to discuss how we can help your business to launch a robust backup and disaster recovery solution. Please contact us.
About Whipcord
For over 2 decades, Whipcord has been delivering confidence to its customers, by providing a suite of optimal IT solutions that include, private cloud, backup, disaster recovery, colocation and network services. Combined with our high-touch support that is unmatched by major providers, we continuously exceed our customer’s expectations and deliver business outcomes, that fuel successful technology strategies for our clients. As a Veeam Gold Partner with data services operations across Canada, we have a wide breath of experience across various industries, that range from national space agencies to small local Canadian businesses.
Whether you’re a part of large corporation or a small business, Whipcord is dedicated to making IT services simple, efficient, affordable and resilient. To learn more about us, please visit https://www.whipcord.com/
-1.png?width=1092&height=792&name=logo%20(1092x792)-1.png)
%20copy(black%20letters).png?width=1092&height=792&name=logo%20(1092x792)%20copy(black%20letters).png)




.png?width=100&height=91&name=white%20logo%20(100x91).png)